OUR KNOWLEDGE BASE

SOLABS’ EQMS (Enterprise Quality Management Software) allows mid-size Life Science organizations to learn from experience, continuously improve and do more with less.
PRODUCTS

QM 10.0
SOLABS QM Essentials
Document Control made simple Document lifecycles: Create, review/approve, revise, and retire documents. All transactions are recorded with e-signatures and timestamps and stored in the Audit Trail.
Audits from start to finish From audit planning to audit preparation and all the way to audit closure, track and document your internal and external audits with the SOLABS QM10 Audit APP.
Intuitive Reporting
Because trending and tracking are so critical to any quality management system, the SOLABS QM Essentials package includes advanced reporting capabilities. The reports and dashboards are available in formats that are easy to use, customizable and share the most common formats, whether it be Excel, PowerPoint, PDF, etc. with anyone within your organization.
Learn more…

QM 10.0
Training Management
Create, assign, schedule and monitor training in a few clicks. Leverage online assessments to validate your team’s learnings. The SOLABS QM Training section allows you to handle all aspects of training, store the related information in a secure, validated system, and easily view the state of compliance by employee, department, training assignment, etc.
Learn more…

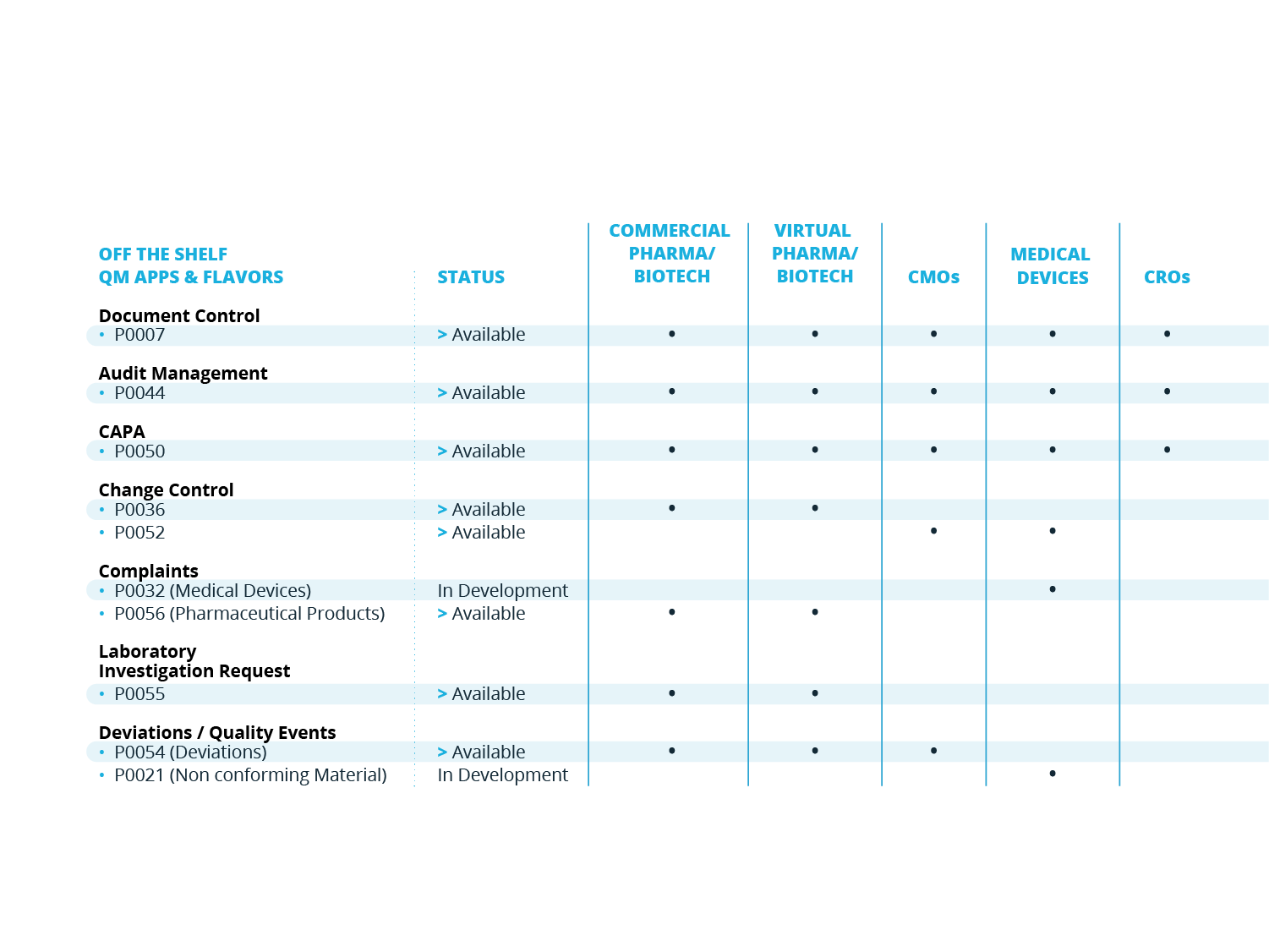
QM APPS
Additional Quality Processes
SOLABS QM is built to scale and grow with your organization. For a smoother and quicker initial implementation, you may start with SOLABS QM Essentials and Training Management for instance, and then implement QM APPs based on priorities.
Customers can purchase additional QM APPs at any time. Our QM APPs are additional quality processes that can be managed through QM10 - always through the same look and feel and functions.
Learn more…
AVAILABLE INTERFACES
SOLABS QM supports Microsoft Azure AD and OneLogin as SSO providers.
A best-of-class interface with Office 365 enables collaborative review on documents.
WE ARE NOT IN A HURRY TO SELL; WE CAREFULLY SELECT OUR CLIENTS!
These are the traditional steps to purchase. We’re happy to support you at every step of the way.

AGGREGATION
PRICING
PRICE TRANSPARENCY
Our pricing model is designed to help clients grow into the software in multiple phases. Document Control and Audit Management are offered as part of SOLABS QM Essentials. Our Training section as well as additional quality processes can be implemented at any time.
Learn more…
RETURN ON INVESTMENT (ROI)
In today's highly competitive environments nobody can afford to make the same mistakes over and over again. Organizations need to learn from experience and capture those learnings in real-time. SOLABS QM10 is built on 15 years of prior experience helping companies do exactly this.
Save time, improve operational efficiency, reduce risk of non-compliance and improve response time for quality processes. SOLABS QM10 is proven to save time for our clients. The calculated ROI is over 80% on average.
SOLABS has more than 5,000 users in a cloud environment and a client renewal rate of 97%. In 2020 across a sample of 20 clients: 145,518 individual training activities were recorded, 20,148 documents were set effective and QM10 allowed for over 6,000 document change controls to be closed.
More on the Total Cost of Ownership (TCO)…
WHAT DO OUR CLIENTS SAY ABOUT QM10?
"SOLABS actually listens to what the customer needs, is in touch with us and is able to adapt their business plan to align with client needs. Lisa Jazon" Ironwood
IMPLEMENTATION
Our Client Success group leads client implementation.
Project timelines range from 3.7 months for our record implementation to 8 months, depending on initial implementation scope and client needs. A detailed project plan is maintained by SOLABS throughout the implementation.
Our services include:
- Project Management
- Validation support
- Configuration Support and Best Practices
- Automated Data Migration (when required)
- Training Workshops
Learn More...
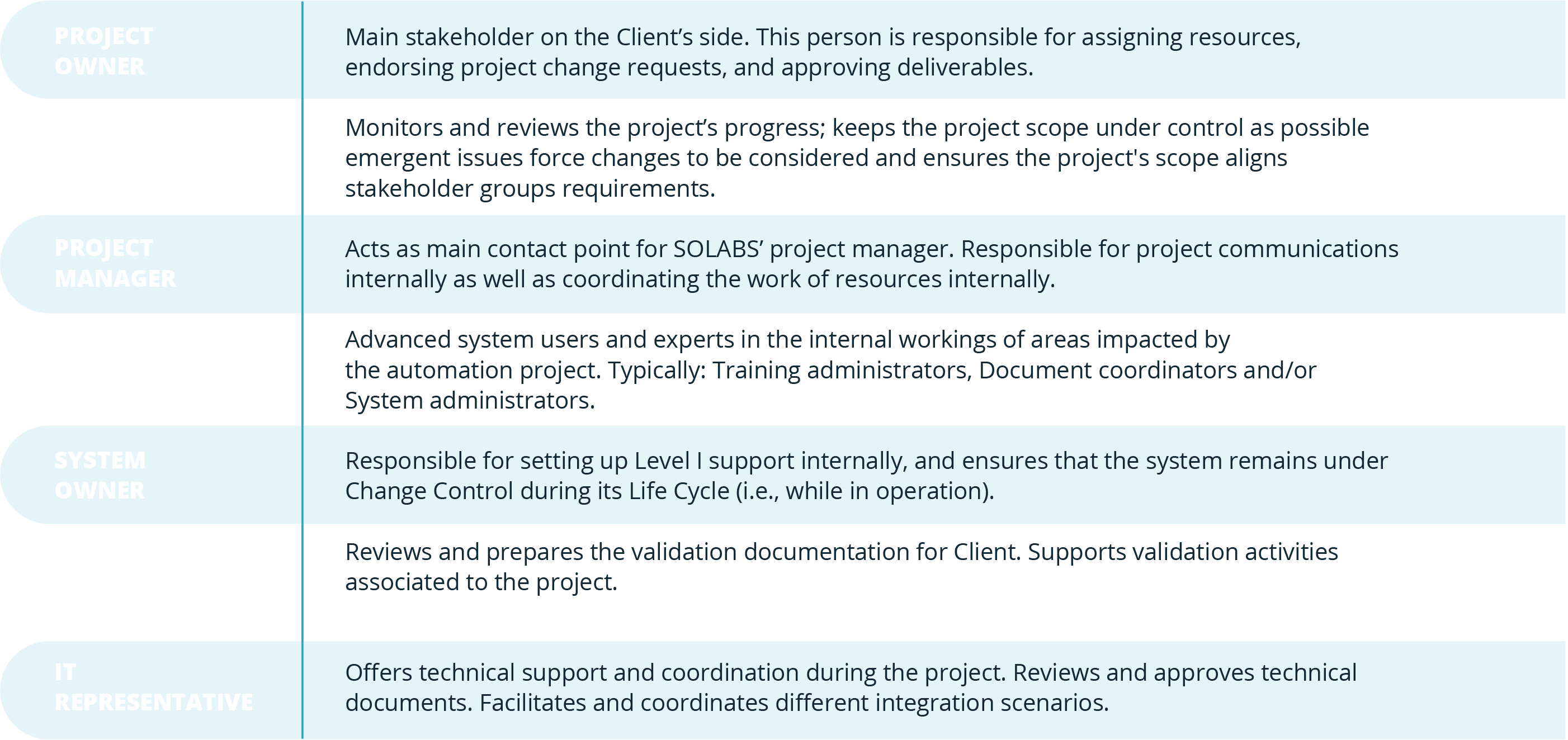
Key roles and responsibilities that are recommended to ensure that SOLABS QM10 remains successful throughout its Life Cycle within your organization.
TECHNICAL SUPPORT & CLIENT SUCCESS ASSISTANCE (CSA)
Level I Support
Unless otherwise agreed in writing by the parties, customers are responsible for providing Level I Support on the Software.
SOLABS can assist and support clients with their internal support through CSA agreements.
More details on Client Success Assistance available from SOLABS
Level II Support
Under its standard agreements, SOLABS provides unlimited Level II Support, namely the detection (off-site) by SOLABS of defects in the Software and providing additional explanations (email, telephone or on-site) to help the Customer use the software appropriately.
More details
ABOUT US
WE ARE OBSESSED WITH DETAILS
Our clients circulate thousands of documents and forms for review and approval yearly. Because of this, even the smallest detail can make the difference between truly achieving time reductions and simply talking about it. We believe that integrating document control, training records and other quality processes under one umbrella is the key to improving operational efficiency.
We are a product of teamwork, with our clients, with our colleagues and partners. We would not exist without our clients; we respect them and have a constant desire to provide the best service for them.
CLIENT MAP
The Avon Company Canada
Client since 2007
Morton Grove Pharmaceuticals
Client since 2012
Eagle Pharmaceuticals
Client since 2014
Tavanta Therapeutics
Client since 2022
Albireo Pharma
Client since 2018
Eurofins CDMO Alphora
Client since 2015
Sobi
Client since 2016
Comanche Biopharma
Client since 2020
LG H&H USA
Client since 2020
MatTek Corporation
Client since 2015
Sterinova
Client since 2013
Purdue Pharma (Canada)
Client since 2006
Bio Agri Mix
Client since 2014
Ironwood Pharmaceuticals
Client since 2015
Cosette Pharmaceuticals
Client since 2023
Arcutis Biotherapeutics
Client since 2019
Trillium Health Care Products
Client since 2015
Reunion Neuroscience
Client since 2021
Innovaderm Research
Client since 2020
Theratechnologies
Client since 2006
Azurity Pharmaceuticals
Client since 2015
Church and Dwight
Client since 2016
Inversago Pharma
Client since 2021
Inversago
Root Instance
Client since 1995
Pillar5 Pharma
Client since 2009
Vita Health Products
Client since 2004
Genvion Corporation
Client since 2017
SOLABS
Client since 1995
MSH Pharma
Client since 2006
UNITY Biotechnology
Client since 2019
Ropack Pharma Solutions
Client since 2008
NKGen Biotech
Client since 2019
Lynden International Logistics Co.
Client since 2022
THOUGHT LEADERSHIP
CONTACT US
Would you like more information about our services?
SALES INQUIRY
Click the chat box icon in the lower right corner to speak directly with someone at SOLABS! Alternatively, fill out the following form and we will get back to you within 24 hours. Or pick-up the phone and reach out a member of our sales department.
CUSTOMER SUPPORT
We offer unlimited Level II Support during business hours (8:00 - 18:00 EST). Authorized contacts can reach support via our support email or by phone at 1-877-322-1368 ext. 911.
1-877-322-1368 ext. 251
CUSTOMER SUPPORT SCHEDULE
Toll free number 1-877-322-1368 ext. 911
Schedule Mon-Fri 8:00 to 18:00 EST
United States, 945 Concord Street, Framingham, Massachusetts, 01701Canada, 9160 boul. Leduc, Suite 410, Brossard, Québec, J4Y 0E3

SOLABS QM (Validation Instance)
Secondary environment mostly used by Super-Users and training purposes.
SOLABS' EROOM
Validation package and related records, SUpport and project documentation.
KNOWLEDGE BASE
Logging in the Knowledge Base allows you to track your questions and conversation history.